Chinese hackers use Google Calendar in stealthy new attack
Google Calendar was used as part of the C2 infrastructure, so users should take care.
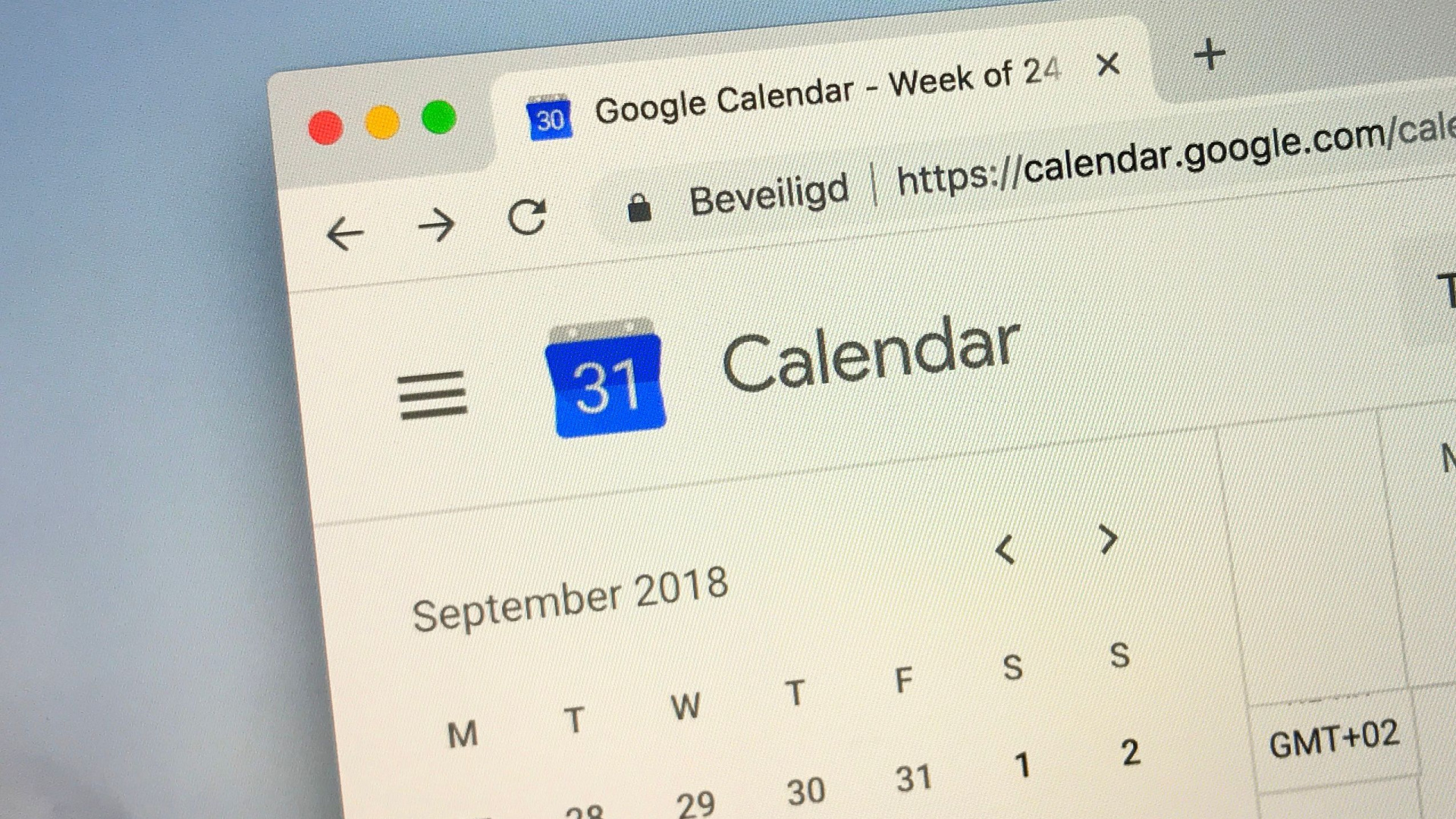
- Google found Chinese hackers abusing Google Calendar
- The service was used to host malicious instructions and to exfiltrate results
- ToughProgress campaign was carried out by Chinese state-sponsored hackers APT41
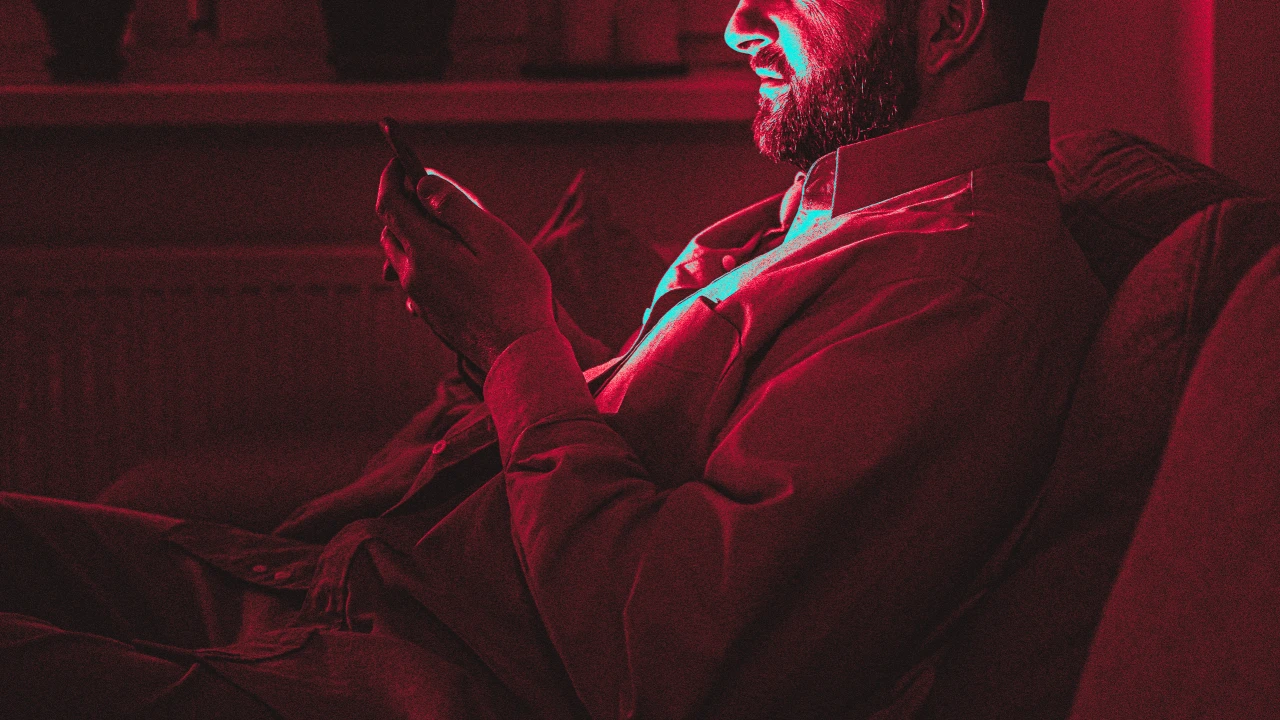
Chinese state-sponsored hackers known as APT41 have been seen abusing Google Calendar in their newest attacks, using it as part of the C2 infrastructure.
Google’s Threat Intelligence Group (TIG) recently discovered the technique, dismantled the setup, and introduced changes to prevent similar attacks in the future.
The attack starts from a previously compromised government website - TIG did not explain how the site was compromised, but said it was used to host a .ZIP archive. This archive is then shared, through phishing emails, with potential targets.
Reading the calendar
Inside the ZIP are three files: a DLL and executable files posing as JPGs, and a Windows shortcut file (LNK) posing as a PDF document.
When the victim tries to open the fake PDF, it runs the shortcut which, in turn, activates the DLL.
This file, in turn, decrypts and launches the third file, which is the malicious payload dubbed “ToughProgress”.
The malware then reads additional instructions shared in two specific events in Google Calendar. The commands are found either in the description field, or hidden events.
To share the results, the malware would create a new zero minute calendar event on May 30, and share the data, encrypted, in the calendar event description.
Since the malware is never actually installed on the disk, and since the C2 communication happens via a legitimate Google service, most security products will have trouble spotting the attack, Google suggests.
To tackle the threat, TIG developed custom detection signatures to identify and block APT41’s malware. It also took down associated Workspace accounts and calendar entries. Furthermore, the team updated file detections and added malicious domains and URLs to the Google Safe Browsing blocklist.
Google also confirmed that at least a few companies were targeted: “In partnership with Mandiant Consulting, GTIG notified the compromised organizations,” it said.
“We provided the notified organizations with a sample of TOUGHPROGRESS network traffic logs, and information about the threat actor, to aid with detection and incident response.”
It did not say how many companies were affected.
Via BleepingComputer
You might also like
- Google warns of legit VPN apps being used to infect devices with malware
- Take a look at our guide to the best authenticator app
- We've rounded up the best password managers